Top 20 Most Destructive Cyber Attacks in History
Generally, I am quite good at techy stuff and I thought I had protection against the malware and spyware, I felt confident that I never have to combat cyber attack. But to my surprise, recently I have been a victim of cyber-attack. Yes, just like anybody else I also had a harrowing experience. I immediately called up one of my best friends Jason, who is well-versed in dealing with cyber attacks and related issues. He really proved helpful in getting me out of this technical ordeal but at the same time he did gave me some tips that will protect me from such attacks in future like setting difficult passwords, clearing browsing history and changing passwords regularly.
As Jason was doing his techy stuff, meanwhile I started a topic of the most destructive cyber-attacks in the history. He said that he has a fair knowledge of the most notorious cyber attacks that have taken place so far. He started by saying that the main culprits behind all this hacking thing are the hackers or ‘hactivists’ (he joked).
1. Flame
He said that Flame tops the list, it is also known as Flamer or Sky wiper. It was a malware that was being made, particularly, to attack computer systems in Middle Eastern countries which were running on Microsoft Windows. The key motive behind designing this virus was ‘espionage’. The worst part was that it further infected all the systems those were on the LAN (local area network) and it engulfed educational institutions, government organizations and private users. It was capable of recording audio, Skype conversation, network traffic, screenshots, etc. CERT (Center of Iranian National Computer Emergency), Kaspersky Lab and CrySys Lab were the organizations behind tracking down the virus.
2. July 2009 Cyber Attacks
These were a succession of attacks and main targets were new agencies, government and financial websites of both South Korea and the United States. This whole process comprised of hijacked computers which made the servers to overload. This was done by the overloading of the traffic known as DDoS attack. The hijacked computers belonged to varied groups such as 18,000 of National Intelligence Service of South Korea, 164,000 of Vietnamese computer security researchers and 48,000 of Symantec’s Security Technology Response Group.
3. Canadian Government Hacking
As per the news sources, the Canadian government also became a victim of a cyber attack in February 2011. It was found the hackers belonged to some foreign nation and they used Chinese IP addresses. Three departments of Canadian government were infiltrated and they were successful in extracting crucial information. Canada had to cut off the internet access of these departments so that no further transmission could be made towards China.
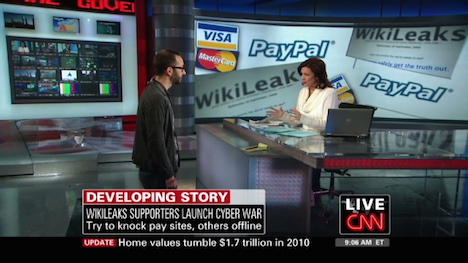
4. PayPal
The cyber attacked took place in December 2010. This attack blocked the account which was operated by WikiLeaks for raising funds. It leads to the mass boycott from the users and it also made the task of the hackers easier.
5. India
Despite being an IT hub, as per a report, India has more than 13,000 security breaches in 2011. However, the major attack that the country has faced took place in 2012 where the hackers successfully gained access to the email accounts of more than 10,000 people; which included high officials from Ministry of Home-Affairs and External Affairs, Indo-Tibetan Border Police (ITBP), Defence Research and Development Organization (DRDO).
6. Stuxnet
This cyber attack took place on June 2010 in Natanz County, Isfahan Province, Iran. The city’s nuclear facility got infected by a cyber worm called Stuxnet. It is believed that this attack was the combined effort of Israel and United States, though nobody took the responsibility of the attack. This worm was responsible for destroying 1000 nuclear centrifuges of Tehran and it also gave a setback to the atomic program as it infected over 50,000 computers as well.
Amidst the discussion, I asked Jason if the needed anything to drink or eat for which he said that he would like to have a beer. I offered him and we had a leisure chat, then we returned to the topic of cyber attacks as it really got me glued.
7. OPI Israel
This cyber attack is believed to be set up by the anti-Israel groups and individuals. OPI Israel is a DDoS assault that took place in April, 2012 on the eve of Holocaust Remembrance Day and the attack’s main motive was to wipe out Israel from the web. Hackers mainly targeted the websites of business and financial sectors, non-profit organizations, educational institutions, privately owned businesses and newspapers in Israel.
8. Operation Aurora
In this cyber attack, Yahoo was targeted and its main origin was from China in an operation was named as Operation Aurora. The main responsibility of the attack was taken by Elderwood Group, based in Beijing and it also had an alliance with People’s Liberation Army. This particular information was disclosed on January 12, 2010, by Google and it has been targeted at varied organizations which included – Adobe Systems, Juniper Networks, Yahoo and Rackspace to gain access and tamper their source code repositories.
9. The Spamhaus Project
Jason said that this cyber attack is considered as one of the major attacks in the history. Spamhaus, is a filtering service that is put into use to separate spam emails, was subjected to cyber attacks. So many Britons use Spamhaus regularly to figure out whether to accept or deny the incoming mails. The attack was so serious that even FBI got involved in this case for further investigations. It was a DDoS (Distributed Denial of Service) attack where a particular website gets flooded with multiple requests, which further results in overwhelming its servers and eventually causing it to crash and in the worst cases it becomes inaccessible for the users.
10. Citigroup
There is no introduction required for Citigroup as it is a major financial giant across the globe. The hackers targeted the company as there are a considerable cash flow and crucial details that flow through the company. The attack took place in 2011, when the contact details and account numbers, of more than 200,000 customers, were compromised. This resulted in a loss of more than $3 million for Citigroup.
11. Heartland Payment Systems
It is a payment processing and technology provider from the US which became the target of Albert Gonzales of Shadowcrew fame, which got access to more than 100 million card numbers. The company had to face a loss of $150 million dollars and moreover it also gave a bad name to the company which promised safest transactions for the users. However, the charges were proved against Gonzales and he was sentenced to 20 years in prison.
12. Hannaford Bros
In 2007, a well-known Scarborough, Maine, United States based supermarket chain suffered a four-month breach wherein more than 5 million debit and card numbers along with other sensitive details were compromised. The hackers installed malware on the servers of the store and the main person behind this was Albert Gonzales. He was also involved in other hacking cases which included – Barnes & Noble, Heartland Payment Systems, Boston Market, and BJ’s Wholesale Club.
13. Operation Shady Rat
A series of cyber attacks took place in 2006 where Operation Shady Rat hit more than 70 organizations across the world which included United Nations, International Olympic Committee. Dmitri Alperovitch was the key person who played a major role in discovering this in 2011 and it was believed that the Republic of China was responsible for this. This operation was derived from the common security industry acronym for RAT (Remote Access Tool) and had main involvement in the cyber attack on the 2008 Summer Olympics as well.
14. TJX
It is a Massachusetts-based apparel and home goods company which was also hacked by Albert Gonzales along with another group of hackers. They were able to gain access to 45 million debit and credit card details which they used for purchasing electronic goods from Wal-Mart. The damages were estimated around $250 million.
15. Sven Jaschan
In 2004 Sven Jaschan, who admitted to being the author of Netsky worms and Sasser computer worms, released a virus that made became a source of frustration for many IT professionals around the world. Though the damage was estimated at $500 million dollars, experts were of the view that it could have been more than that as the computer systems of Delta Airlines were disabled. This led to the cancellation of various transatlantic flights. A bounty worth $250,000 was placed on his head and he got arrested after a three-month manhunt operation.
16. Michael Calce
He is also known as Mafiaboy on the internet and he was a cyber-superstar. He was responsible for conducting varied attacks on some of the prominent companies having high security. Calce attacked media major CNN, Amazon, Ebay, Dell and lots more and the damages were estimated at $1.2 billion dollars. He was sentenced to eight months.
17. Presidential-Level Espionage
The computers, used in the campaigns of John McCain and Barack Obama, were attacked during the presidency run 2008. As per this breach, the hackers gained access to the sensitive data and important emails used in the campaign. Seeing this breach, FBI confiscated all the phones, computers and electronic devices used in the campaign.
18. Sony
In 2011, 77 million Playstation network and Sony Online Entertainment accounts, which comprised of credit & debit card details were stolen by the cyber hackers. This breach was estimated around $2 bn dollars and the worst part of this hacking was the hackers were able to log on while the company was trying to fix the breach which took around 25 days.
19. Epsilon
It is considered as the costliest cyber-heist of all time which involved Epsilon, largest provider of marketing and handling service and some of their major clients are JP Morgan Chase and Best Buy. The hackers targeted the email addresses to serve their felonious intentions and the losses were estimated at $4 billion.
20. The Original Logic Bomb
During the cold war in 1982, the CIA managed to find a method through which they can disrupt the Siberian gas pipeline of Russia without using any conventional explosives like bombs and missiles. The method they used was known as ‘Logic Bomb’ and the entering of a portion code in the computers that oversees the pipeline, which led to the computational chaos.
Well, I have to admit I got intimidated by all this discussion. Jason said that I need to be cautious about the passwords and he also shared some key tips that can save me from any probable hacking episode.
Tags: cyber attack, hacking, internet, it knowledge, privacy & security